Bots racked up a thousands-dollar bill overnight — how to avoid it
A developer on Reddit got a bill for thousands because of bots. I looked at my own code and realized I was in the same spot.
I came across a post on Reddit from a developer. He launched a SaaS app that called AI models — similar to GoStylo. One morning he opened his email and there it was. A bill for several thousand dollars. For one night.
Bots. Hundreds of different IP addresses, each within the free tier limit, but together they ate through his entire monthly budget in a few hours.
I looked at my own code and realized I was in the exact same situation.
What was wrong
My rate limiting was based on fingerprints — IP address plus a few browser headers. Each fingerprint was allowed 6 requests per hour. But a bot with a thousand different IPs means a thousand fingerprints. A thousand times six is six thousand requests per hour. Each one calling an AI model. Each one costing real money.
Worse, 10 out of 12 API endpoints had no rate limiting at all. A bot could spam the database, exhaust authentication — and I wouldn't find out until the bill arrived.
What I did about it
I went with a layered approach. Not one big wall, but several smaller ones, each catching a different type of attack.
Middleware — before a request even reaches any code. A limit of 200 requests per minute per IP (no human hits that, bots do), blocking known bot tools by their User-Agent header, and a whitelist for search engines so I don't wreck my SEO. Plus caching on static pages — when a bot hammers the blog a thousand times, it gets the same cached page every time. Zero server load, zero cost.
Rate limits on every endpoint — I went through all of them and set limits based on sensitivity. Public endpoints 60 per hour per IP, authenticated reads 120, writes 60, account deletion 5. Before that, there was literally nothing.
Bot scoring on the transform endpoint — that's the one calling AI models, the one that costs money. Each request gets a score based on how much it looks like a bot. A filled honeypot (a hidden form field that humans never see but bots fill automatically), a missing cryptographic signature from the frontend (meaning someone's calling the API directly), 5 requests in 5 seconds from the same source — each signal adds points. Low score slows the request down, medium triggers a CAPTCHA (solve it once, you're good for 24 hours), high score blocks it.
Cost tracking — not just the number of requests, but how much they actually cost in dollars. A bot doesn't need to send many requests, it just needs to send long texts. When a fingerprint burns through its hourly budget, it's done.
Monitoring — an automatic check every 15 minutes on overall traffic. When anonymous requests hit 80% of the limit, I get a notification. I don't want to find out about an attack over morning coffee.
Nothing changed for regular users
No CAPTCHA during normal use, no slowdowns. If you use GoStylo normally, you'll never run into any of this.
That Reddit post made me look at security before it was too late. Better to spend a few days on prevention than to wake up to a bill worth thousands.
Ready to improve your writing?
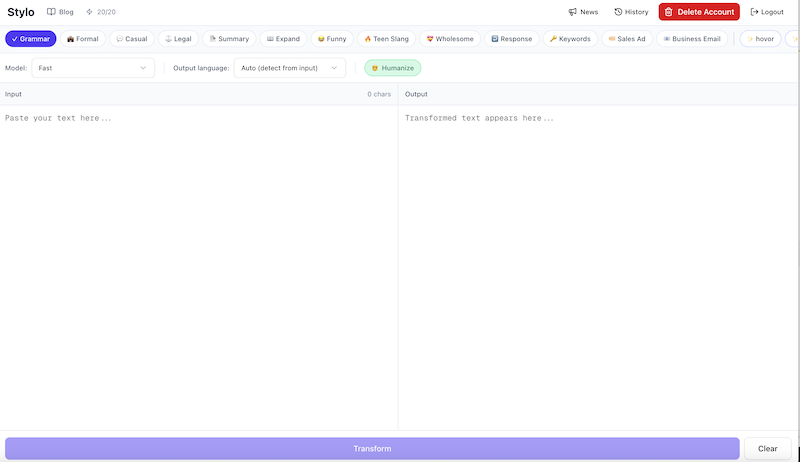
Try Stylo for free and experience AI-powered writing assistance that adapts to your style.
Try Stylo FreeRelated Posts
Writing in a Foreign Language Without Stress: How to Use Stylo for Emails in German or English
Write an email in your native language and Stylo translates it into German, English, or any other language. No stress, no Google Translate.
product updatesStylo for Android: From Idea to Release
After months of development and optimization, Stylo for Android is finally ready for testing. Here's what it took to build it.